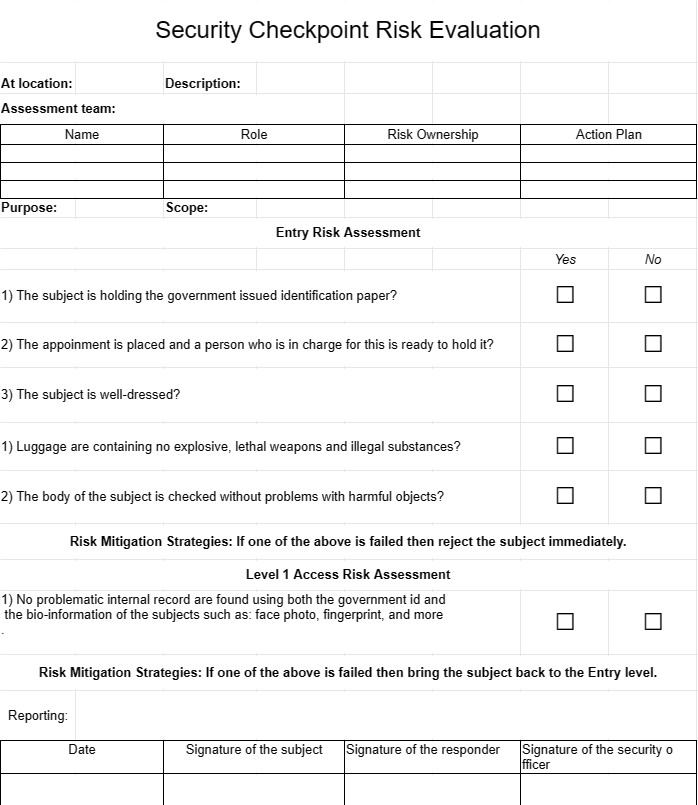
Security Checkpoint Risk Evaluation
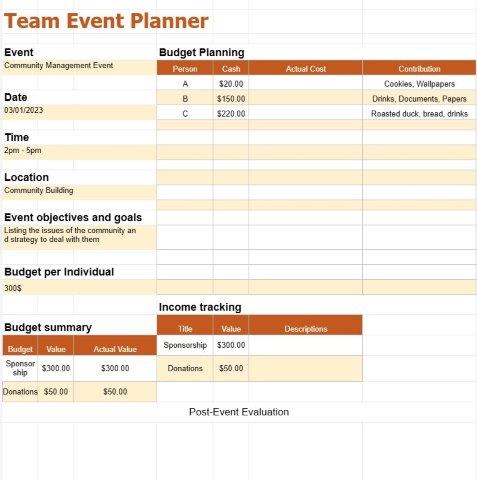
Category : Planners
Letting individuals in and out of a position is a complicating task nowadays, this is a fundamental tool for security man at a checkpoint to manage all of the risks which can be involved with an individual.
The Security Checkpoint Risk Evaluation Template is an essential document used in security management and risk assessment. It is particularly valuable in contexts where security checkpoints or access control points are involved, such as airports, government facilities, corporate campuses, and critical infrastructure sites. This template serves as a structured framework for evaluating and mitigating security risks at these locations.
Let's explore the key components and elements typically included in a Security Checkpoint Risk Evaluation Template:
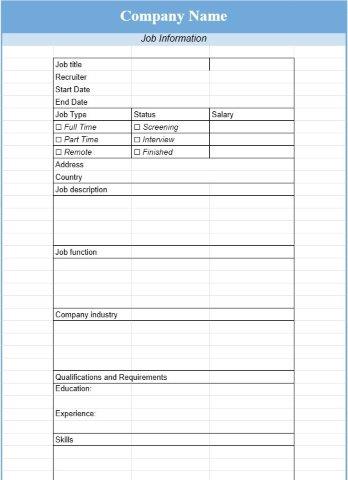
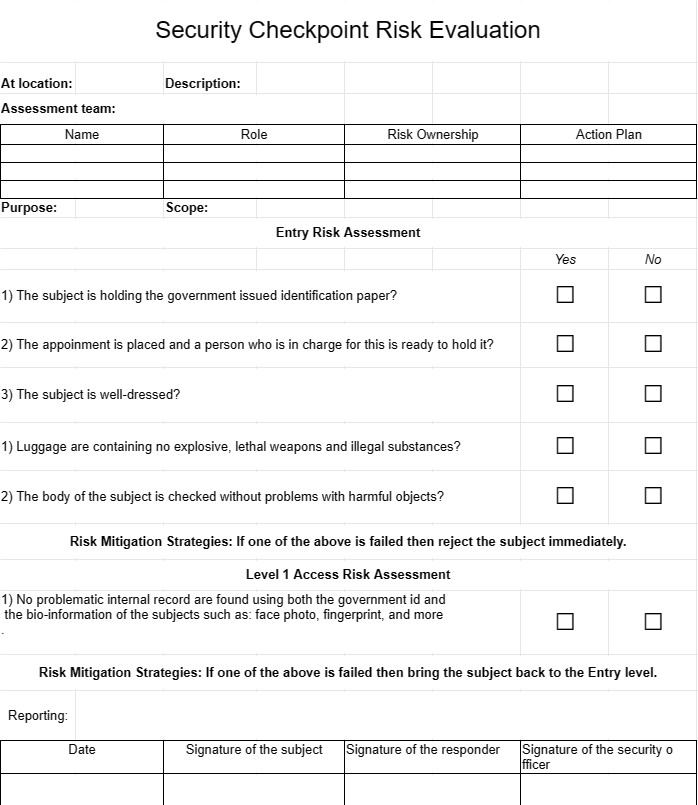
- Location and Checkpoint Information: The template starts by identifying the specific location and security checkpoint under evaluation. This includes details such as the checkpoint's name, description, and geographical location.
- Assessment Team: A crucial aspect of risk evaluation involves the assessment team. The template includes a section to list the names and roles of team members responsible for conducting the assessment.
- Purpose and Scope: It outlines the purpose and scope of the security checkpoint risk evaluation. This section sets the context for the assessment and defines what is being assessed and why.
- Risk Categories: Security risks often fall into different categories, such as physical security, personnel security, information security, and operational security. The template provides space to categorize risks for more focused evaluation.
- Risk Identification: A comprehensive risk evaluation begins with risk identification. The template includes fields for listing potential risks, vulnerabilities, and threats specific to the security checkpoint in question.
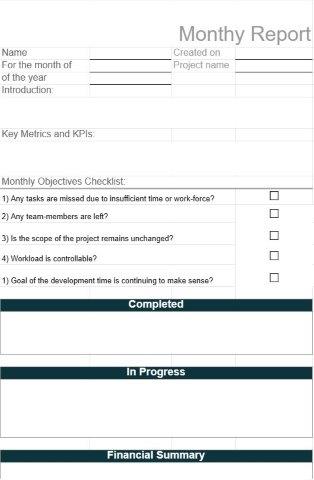
- Risk Assessment: Each identified risk is assessed in terms of its likelihood of occurrence and the potential impact it could have. These assessments help prioritize risks based on their severity.
- Risk Mitigation Strategies: For each identified risk, the template provides space to outline mitigation strategies and measures. These strategies may include security enhancements, procedural changes, or training initiatives.
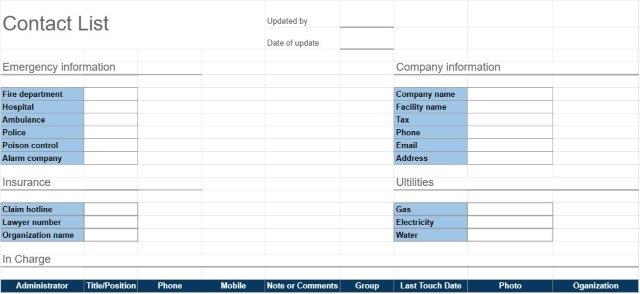
- Risk Ownership: Assigning ownership of each risk to responsible individuals or teams ensures that someone is accountable for monitoring and managing the risks.
- Action Plan: The template allows for the development of action plans, detailing the steps to be taken to address and mitigate identified risks.
- Monitoring and Review: An effective security checkpoint risk evaluation is an ongoing process. The template includes provisions for regular monitoring and review of risks to assess the effectiveness of mitigation efforts.
- Documentation: Comprehensive documentation is crucial for accountability and compliance. The template serves as a record of the risk evaluation process, including assessments, actions taken, and outcomes.
- Reporting: The findings of the security checkpoint risk evaluation are often summarized in a report. The template may include a section for documenting key findings and recommendations for improving security.
The Security Checkpoint Risk Evaluation Template serves several essential purposes:
- Security Enhancement: By systematically assessing risks and vulnerabilities, organizations can implement measures to enhance security at checkpoints and access control points.
- Risk Mitigation: The template facilitates the development of mitigation strategies that reduce the likelihood and impact of security breaches or incidents.
- Compliance: In some industries or regulatory environments, regular security risk assessments are required for compliance purposes.
- Resource Allocation: Organizations can allocate resources more effectively by focusing on the most critical security risks.
- Continuous Improvement: Regular monitoring and review ensure that security measures remain effective and adaptable to changing threats.
In summary, the Security Checkpoint Risk Evaluation Template is a vital tool for organizations concerned with security and risk management. It enables systematic assessment, mitigation, and documentation of security risks, ultimately contributing to the safety and security of individuals and assets at access control points.
Easy Preview and Download Spreadsheet Template
View the full version of a spreadsheet template with no limitations to see if you like it then you can download the excel template to store it on your device and use it for free.
Access Spreadsheet Template from Anywhere
This is working on all popular operating system such as Windows, MacOS, Linux, iOS. You can see the spreadsheet templates and download them without additional programs.
How to use a template
Figure out how to preview, download and then use the spreadsheet template by following the steps which are extremely easy to follow
More similar templates
See more of the spreadsheet templates which are under the same category with the chosen one.